Why a Password Alone Isn’t Enough
Like most people, you probably use a strong password to protect your accounts. But hackers use different tactics to steal or guess your passwords.
- Hackers use phishing attacks to trick you into giving up your login credentials.
- Scammers buy credentials stolen in data breaches, using your username and your password to log in to the account where the breach happened. (That’s why it’s important to change your password right away if you find out that your information may have been exposed in a breach.)
- Hackers might also try to use the username and password to log in to another one of your accounts. This works only if you use the same username and password in more than one place — and is a reason to never reuse the same username and password.
- If hackers only have your username, they can use software to guess your password. If the site doesn’t have safeguards to detect this type of attack, the hacker’s software may be able to try many different passwords.
Taking steps to keep your password secure is an important first line of defense against hackers. But the best way to protect your accounts is to use two-factor authentication, sometimes called two-step verification or multi-factor authentication.
Protecting Your Accounts
To prevent unauthorized access to your accounts, sites usually require you to sign in with a username and password. This process verifies who you are and is known as authentication. The credential you give to log in — your password, in this example — is a type of authentication factor. Authentication factors fall into three categories:
- Something you know, like a password, a PIN, or the answer to a security question.
- Something you have, like a one-time verification passcode you get by text, email, or from an authenticator app; or a security key.
- Something you are, like your fingerprint, your face, or your retina.
Accounts with two-factor authentication require you to enter a credential from two of the three categories to log in.
Two Factors Are Better Than One
Using only one factor — say, something you know, like a password — to log in to your account is like having one lock on your front door. And not a very secure one.
Using two-factor authentication is like using two locks on your door — and is much more secure. Even if a hacker knows your username and password, they can’t log in to your account without the second credential or authentication factor.
The Most Common Methods of Authentication
More and more sites and apps are offering two-factor authentication. Some let you choose which authentication method to use. Others only give you one option. These are some of the most common authentication methods out there.
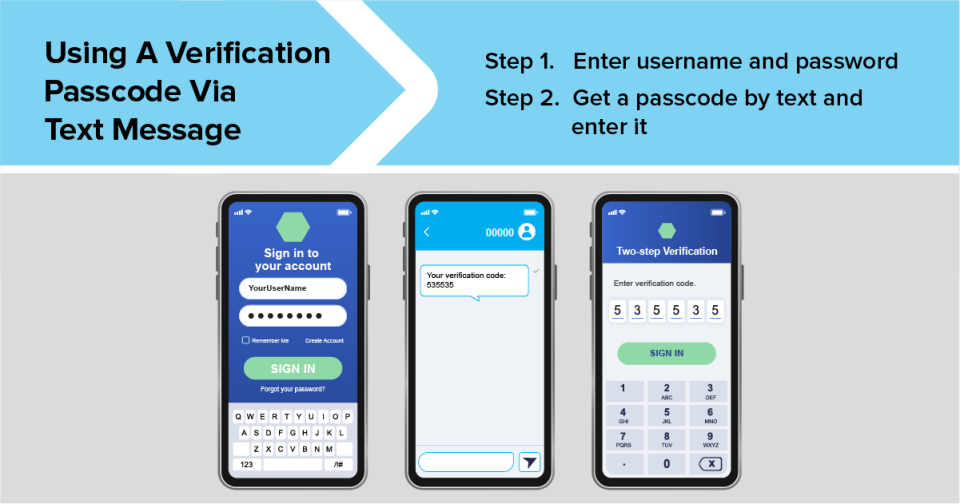
1. One-time passcode via text message or email
With this type of authentication, you get a verification passcode by text message or email. It’s typically six digits long but can be longer. It’s only good for one log in and expires automatically.
Getting a passcode by text message is a common and simple method of authentication that only requires a phone that can get text messages. But it has its drawbacks. Hackers can take over your phone number through a SIM card swap attack and get text messages sent to your number, including those with a verification code, before you realize someone stole your number.
If you get a verification passcode by email, use a strong password and two-factor authentication on your email account. That’ll make it harder for someone to hack into your email and steal your one-time passcode.
Scammers try to trick you into giving them your verification passcode. No matter what the story is, don’t share your verification code with someone if you didn’t contact them first.
If getting a verification passcode by text message or email is the only option the account offers, it’s better than nothing. But it’s safer to use an authenticator app or security key, if they’re an option.
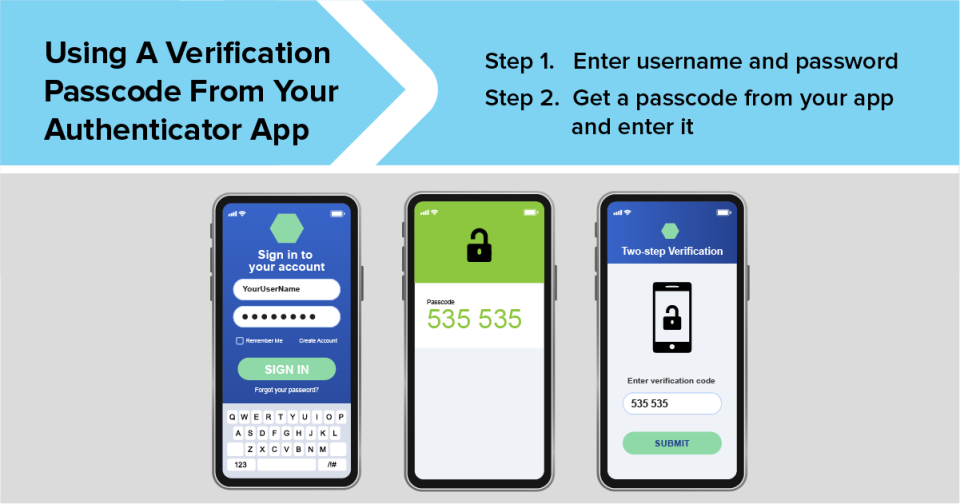
2. An authenticator app
Some accounts let you use an authenticator app on your phone or tablet to verify it’s you trying to log in. There are several authenticator apps out there, like Google Authenticator, Microsoft Authenticator, and Duo.
Authenticator apps typically generate a verification passcode, like one you might get by text message or email. But using an app is safer because the passcode isn’t susceptible to a SIM card swap attack or to someone hacking your email.
An authenticator app may also give you the option to get a push notification on your phone or tablet every time someone tries to log in to your account. The notification might give you some details about the login attempt, like the account someone is trying to log in to, their physical location, the type of device they’re using, and the date and time of the login attempt. You can approve or deny the request with a tap.
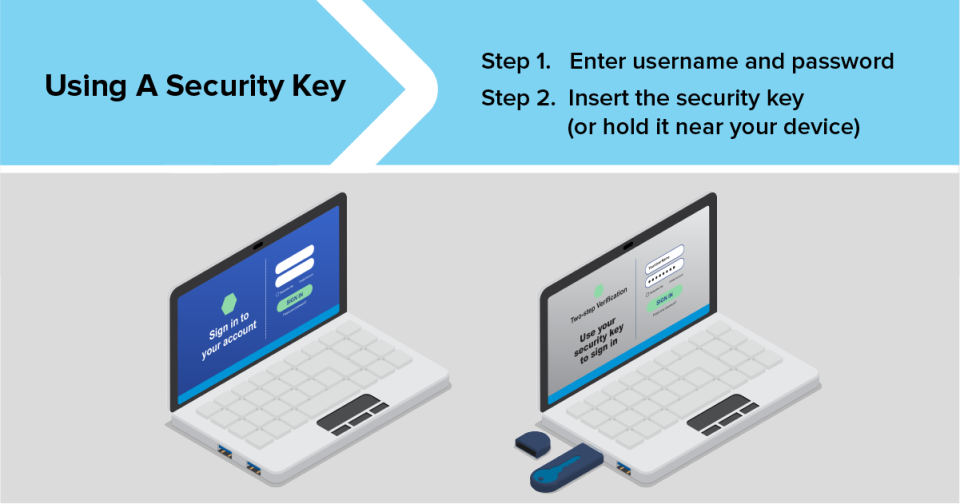
3. A security key
Security keys are physical devices that you use as your second authentication factor. They come in different shapes and sizes. You can buy one for personal use or you might get one from your employer.
Security keys use encryption to confirm that the key is associated with your account. Some plug into a USB port. Others use near-field communication (NFC) to connect to your device when you hold it close. Security keys are the strongest method of two-factor authentication because they don’t use credentials that hackers can steal.
Turning On Two-Factor Authentication
More and more sites and apps are offering two-factor authentication, but it’s not usually on by default. To turn it on, go to your account settings, look for two-factor authentication, two-step verification, or multi-factor authentication, and follow the steps.
Start with your most sensitive accounts, like your bank, credit cards, email, social media, tax filing website, and payment apps. Then add it to other accounts, like sites you shop on.
After you set up two-factor authentication, you may have the option to remember the device you’re using to log in. If you do, instead of having to give the second credential every time you log in, you may only need to do so in certain situations, like when you log in from another device. Only have the account remember your own devices. Don’t have it remember the device if you’re logging in from a public computer, like at a library.
Two-factor authentication can add an extra layer of security that protects you from hackers. And spending a few minutes to turn it on now can save you the hassle — and countless hours — it’ll take to recover a hacked account or deal with identity theft.